Julian's Portfolio
About Me

I’m Julian Ramirez, an IT Support Technician and aspiring SOC Analyst based in Los Angeles.After several years in client-facing B2B SaaS sales and relationship management, I shifted my focus toward cybersecurity where I combine technical problem-solving with communication and business insight.I’ve built hands-on experience in areas like network security, threat prevention, and cloud access management through real Palo Alto Networks and AWS lab environments.My goal is to protect systems and people by designing secure, efficient solutions that scale.
Project: Threat Prevention & Real-Time Monitoring (Palo Alto Networks PA-440)
Environment
Palo Alto Networks PA-440 | PAN-OS 11.2 | Threat Prevention + Anti-Spyware + Vulnerability Protection Subscriptions | Local Lab NetworkOverview
In this project, I configured and monitored Palo Alto Networks’ Threat Prevention suite to identify, block, and analyze malicious traffic patterns in a lab environment.
The goal was to simulate how enterprise firewalls detect and respond to intrusion attempts, malware downloads, and C2 communications in real time.Step-by-Step Implementation1. Enabled Threat Prevention Profiles
Activated Intrusion Prevention (IPS), Anti-Virus, Anti-Spyware, and Vulnerability Protection features.
Attached these profiles to outbound and inbound rules to ensure full traffic inspection.
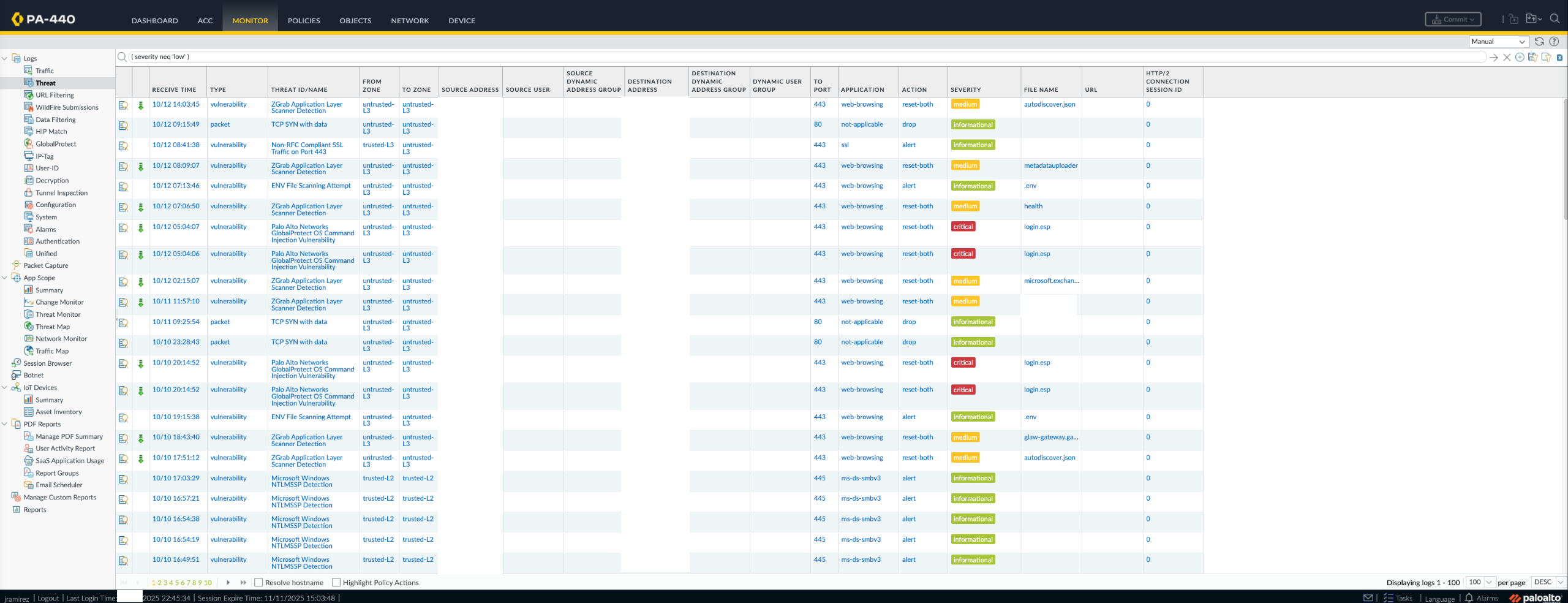
2. Monitored Threat Logs
Navigated to Monitor → Threat, filtered by severity (Low → Critical), and reviewed detections such as:
- ZGrab Application Layer Scanner Detection
- Non-RFC Compliant SSL Traffic
- EVN File Scanning Attempt
- TCP SYN with data anomalies
Each log captured source zone, destination, port, and action (e.g., reset-both, alert, drop) — illustrating real-time firewall response.3. Analyzed Blocked Threats
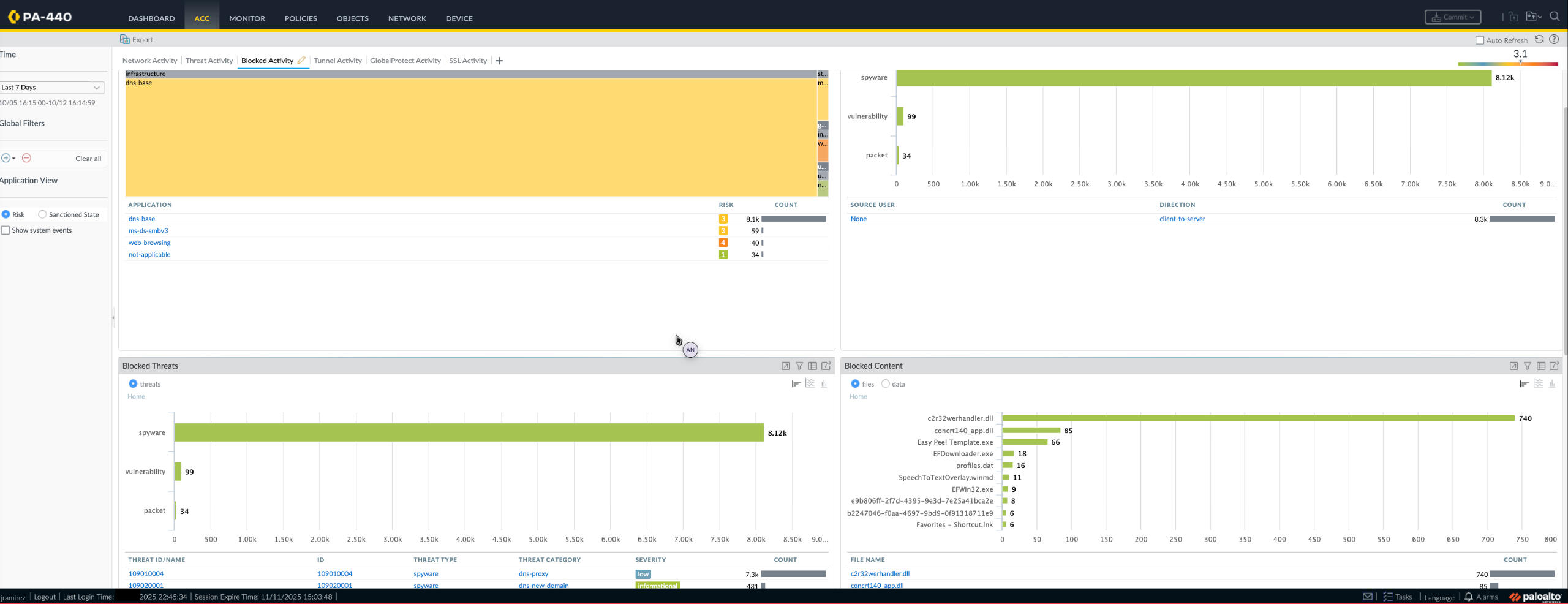
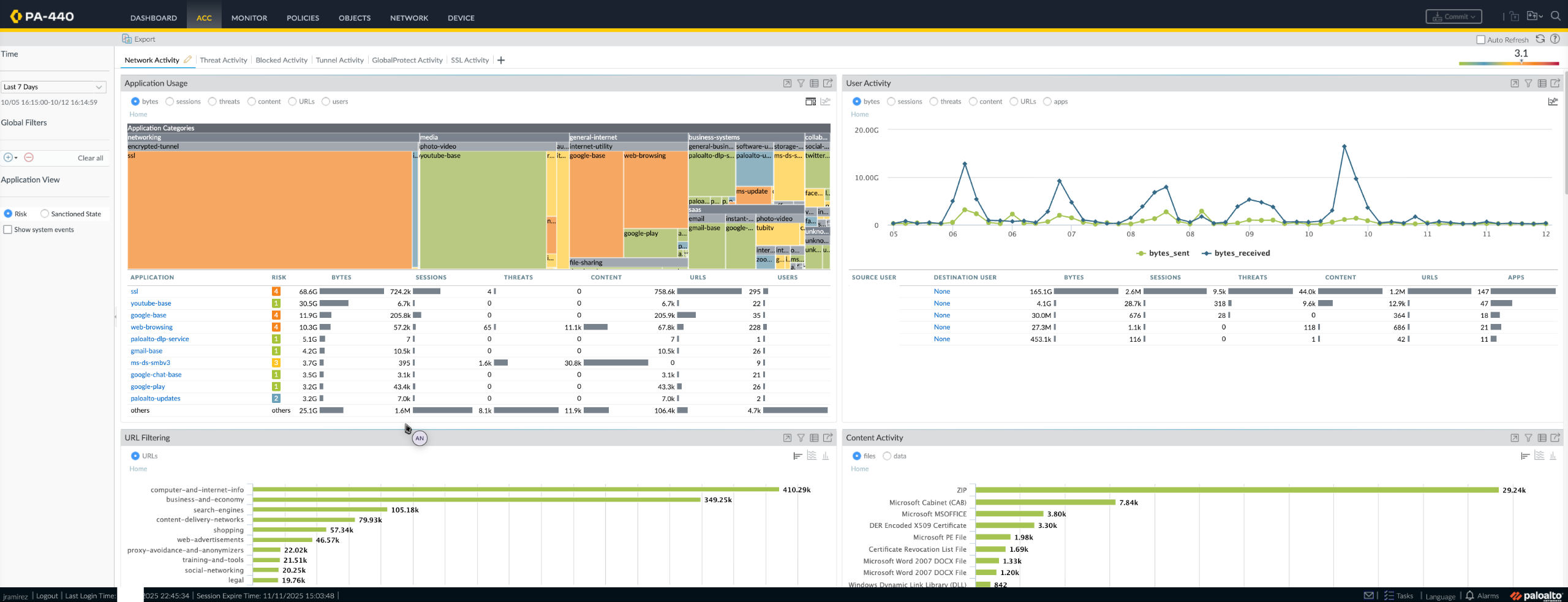
Used the Application Command Center (ACC) to visualize detections by threat type (Spyware, Vulnerability, Packet).
Over 8 000+ spyware detections and 99 vulnerability events were captured within 7 days.
5. Report Generation & Export
Exported Threat Logs to CSV and produced summary reports showing trends by threat type and source.Challenges & Lessons Learned
Low-severity events initially overwhelmed visibility, so I applied custom log filters: (severity eq critical) or (severity eq high) and scheduled exports for deeper Excel analysis.
Also learned that policy order and profile attachment are critical — if profiles aren’t linked correctly, traffic bypasses inspection.Outcome
Demonstrated the ability to deploy and operate Palo Alto Threat Prevention in a simulated enterprise setting.
Developed skills in reading, filtering, and correlating logs — core capabilities for SOC monitoring and Tier-1 analysis.Visual Summary
1. Threat Monitor → real-time log feed
2. ACC Blocked Activity → visual analytics of blocked events
Project: Firewall Policy & NAT Configuration (Palo Alto Networks PA-440)
Environment
Palo Alto Networks PA-440 | PAN-OS 11.2 | Layer-3 Enterprise SimulationOverview
In this project, I built and tested firewall rules and NAT (Network Address Translation) on a Palo Alto PA-440 device.
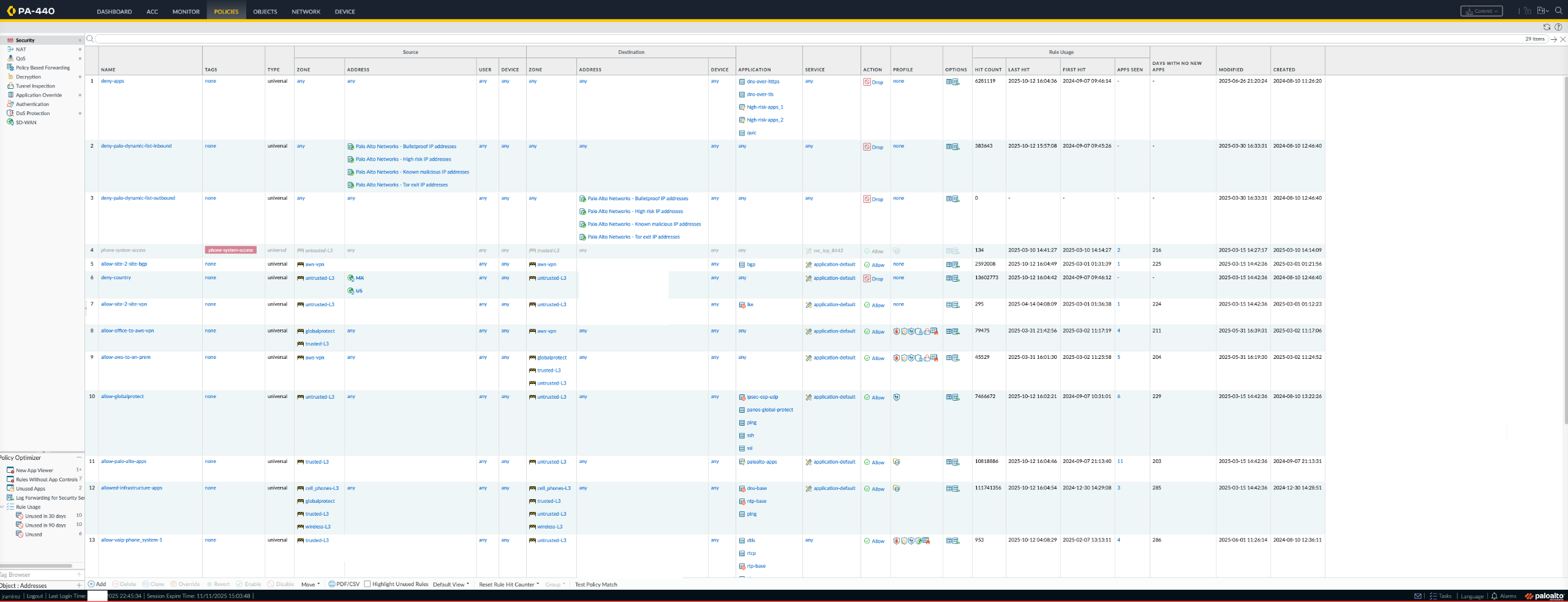
The goal was to show how businesses safely control what traffic enters and leaves their network — like putting digital “doors and locks” between trusted and untrusted areas.Step-by-Step Implementation1.Designed Security Policies
Created firewall rules based on the principle of least privilege, meaning only the traffic that truly needs access is allowed.
- Allowed safe outbound web traffic (HTTPS/HTTP)
- Limited inbound traffic to only SSH (secure management access)
- Denied all other unknown or risky connections
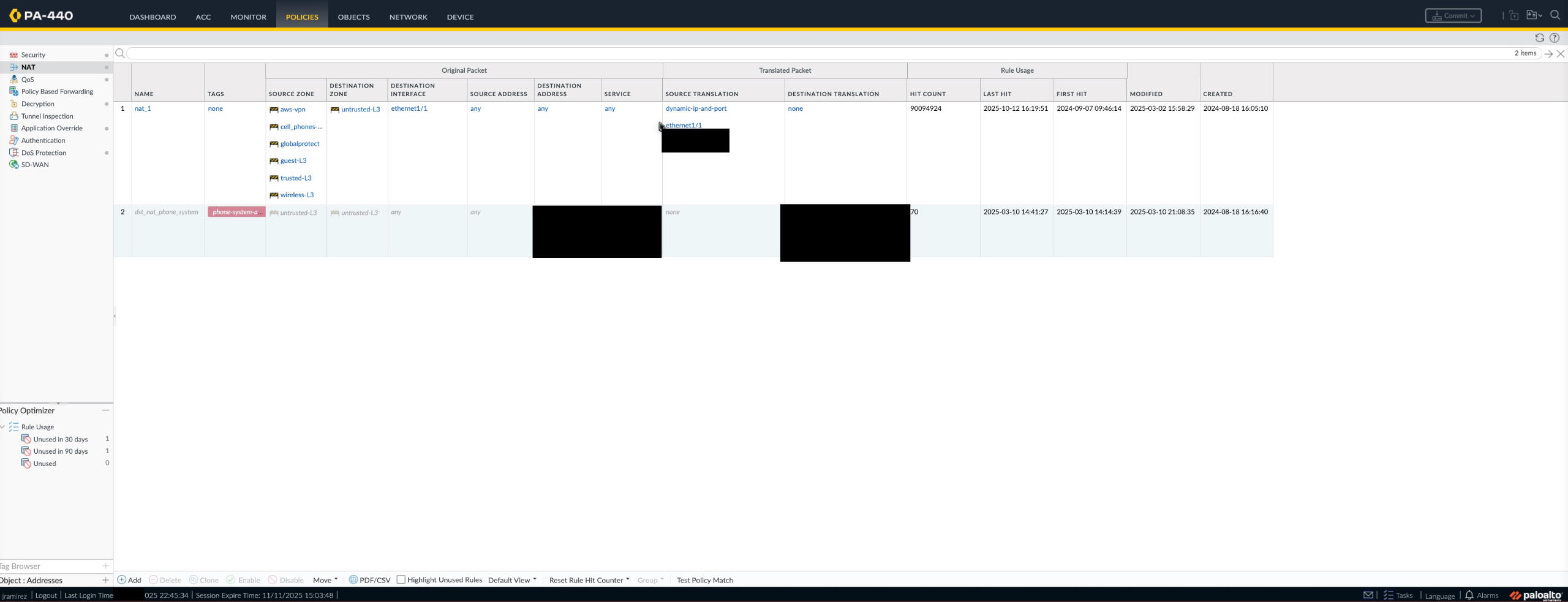
2. Configured NAT (Network Address Translation)
Set up both Dynamic NAT (for users browsing the internet) and Static NAT (for inbound access to specific systems).
This lets internal IP addresses stay private while still allowing internet access — similar to how a phone hides your personal number when you call from work.
3. Tested Traffic Flow
Verified that trusted users could reach the web while outside sources couldn’t reach internal systems.
This setup mimicked how enterprises segment their networks to reduce attack surfaces and protect sensitive data.
Outcome
The final configuration showed how firewall rules and NAT work together to control data flow and keep a network safe.
I learned how to balance security and accessibility, ensuring that users stay protected while business traffic keeps moving.Skills Gained: Security policy design, NAT translation, traffic segmentation
Project: URL Filtering & Application Control (Palo Alto Networks PA-440)
Environment
Palo Alto Networks PA-440 | PAN-OS 11.2 | Threat Prevention + URL Filtering SubscriptionOverview
In this project, I set up Palo Alto’s App-ID and URL Filtering features to help control what users can access on the web.
The goal was to protect the network by blocking risky sites—like gambling, adult content, and social media—and to show how the firewall identifies traffic by application, not just by port or protocol.
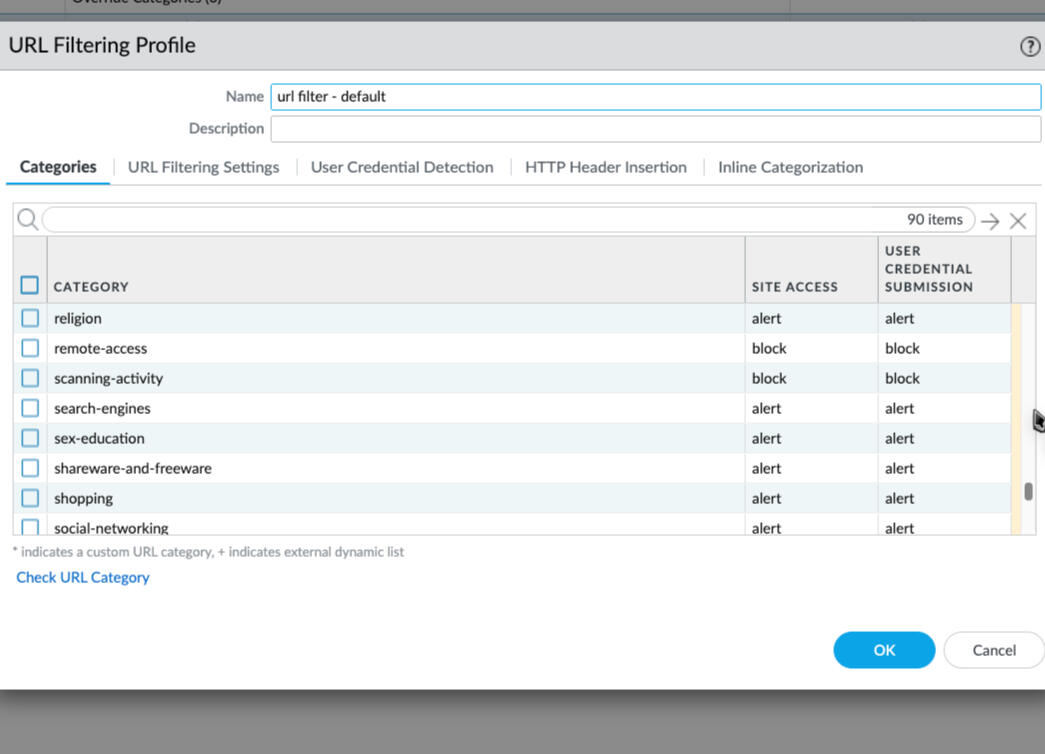
This project simulated how a company can stop unsafe or non-work-related traffic before it ever reaches users, while still allowing safe browsing and business applications.Step-by-Step Implementation1. Created URL Filtering Profiles
Configured filtering profiles to block specific web categories such as Adult, Gambling, and Social Media, while allowing safe and verified sites.
Each category was assigned an action (allow, alert, or block) and linked to my outbound security policy.
2. Enabled App-ID Inspection
Turned on Application Identification (App-ID) to analyze traffic based on the actual application, not just the port number.
This allowed the firewall to recognize when users tried to use alternate ports or encrypted channels to bypass restrictions.
The system adapted automatically—blocking the application even when it hid behind standard web traffic.
Outcome
This configuration demonstrated how next-generation firewalls inspect traffic deeply—using both application and content awareness—to protect against risky behavior and maintain company productivity.
It also reinforced how App-ID and URL Filtering work together as a layered defense strategy:
- App-ID controls what is being used.
- URL Filtering controls where users go.Skills Gained: Application-aware security, web category filtering, adaptive inspection
Project: GlobalProtect VPN Deployment (Palo Alto Networks PA-440)
Overview
Configured a GlobalProtect VPN gateway to enable secure, encrypted remote access for users connecting from outside the corporate network.
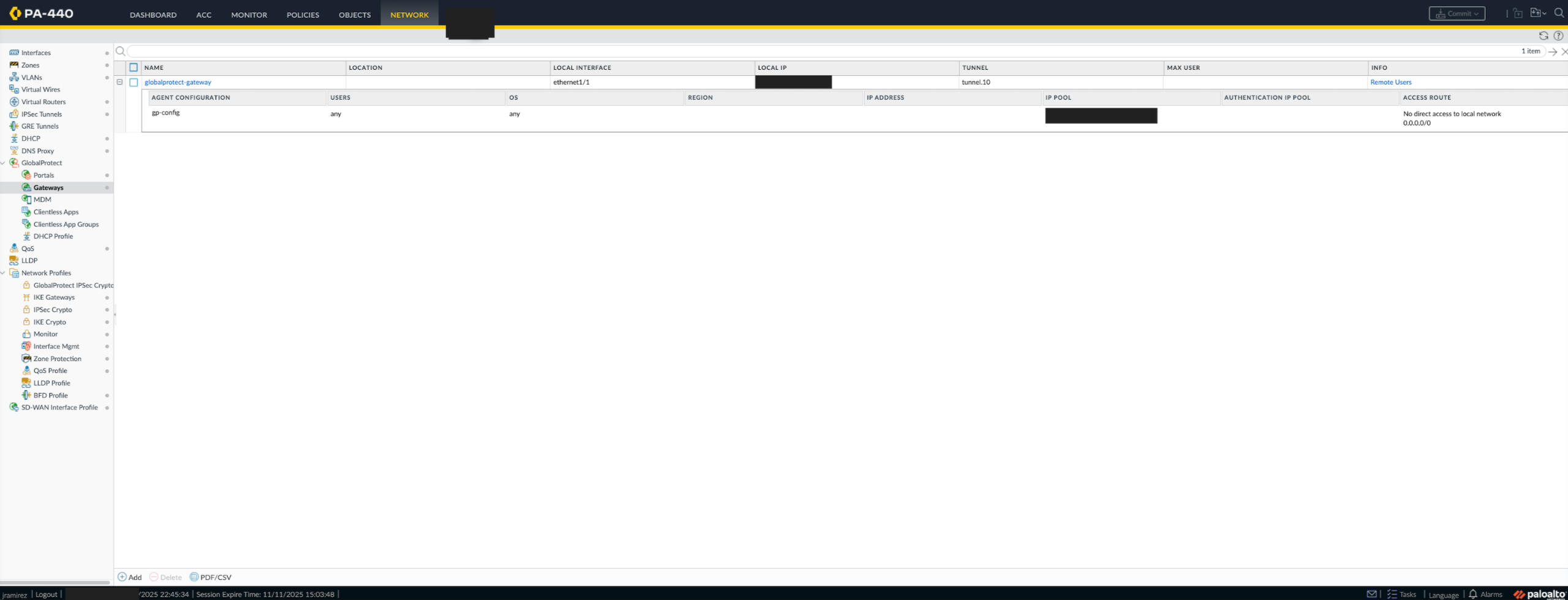
The goal was to simulate how businesses support hybrid work, allowing employees to connect safely to internal systems from remote locations.Step-by-Step Implementation1. Created Tunnel Interface & IP Pool
Defined a new tunnel interface (tunnel.10) under the Network tab and assigned it to ethernet1/1.
Configured an IP address pool to provide unique, dynamically assigned IPs to remote VPN users once connected.2. Configured the GlobalProtect Gateway
Navigated to Network → GlobalProtect → Gateways and created a gateway profile named globalprotect-gateway.
Attached it to the tunnel interface and configured:
- Authentication: Local username/password for lab testing
- Encryption: SSL enabled for secure data transmission
- Access Route: 0.0.0.0/0 to allow full-tunnel routing through the firewall
2. Enabled App-ID Inspection
Turned on Application Identification (App-ID) to analyze traffic based on the actual application, not just the port number.
This allowed the firewall to recognize when users tried to use alternate ports or encrypted channels to bypass restrictions.
The system adapted automatically—blocking the application even when it hid behind standard web traffic.
3. Applied Firewall Rules
Created security policies that allowed only VPN traffic to trusted internal zones while blocking unauthorized access.
Applied the principle of least privilege, ensuring users could only reach necessary resources.4. Verified Connectivity & Logging
Connected from a remote test client and verified tunnel establishment under Monitor → Traffic.
Confirmed successful IP assignment, encryption status, and policy enforcement logs.Challenges & Lessons Learned
Initially faced issues where users could not connect because the tunnel interface was not properly mapped to the correct security zone.
Resolved it by updating zone assignments and re-binding the gateway to the tunnel interface.
Learned how GlobalProtect uses SSL for session establishment and IPsec for ongoing data encryption, providing both security and performance.Outcome
Successfully demonstrated the ability to deploy and manage a secure VPN solution using Palo Alto Networks GlobalProtect.
Developed hands-on experience in:
- Encryption protocols (SSL/IPsec)
- Remote access configuration
- Security policy design and verification
Project 5: Cortex XDR — Incident Investigation and Threat Hunting
Environment
Cortex XDR | Palo Alto Networks Cloud Tenant | XQL Query Builder | WildFire Threat IntelligenceOverview
Used Palo Alto Cortex XDR to perform a hands-on incident investigation that simulated a real SOC analyst workflow.
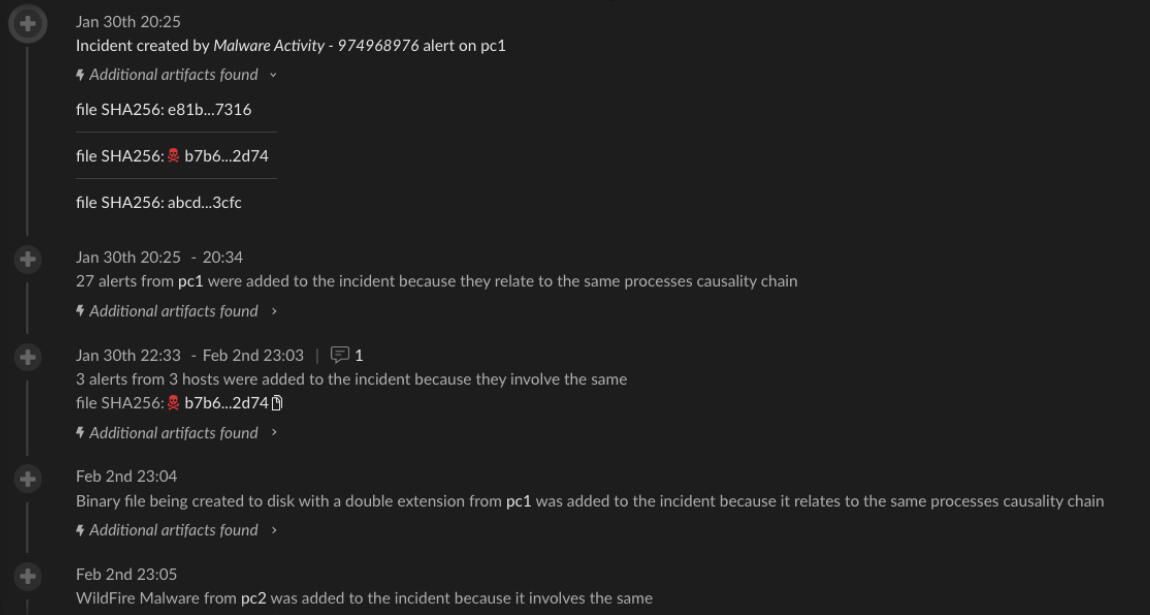
The objective was to identify, analyze, and trace a malware infection across multiple hosts, practicing alert triage, root cause analysis, and data correlation using XQL queries.Step-by-Step Implementation1. Incident Overview
Reviewed a Malicious Activity Incident (ID-3572) in the Cortex XDR console, which displayed mapped MITRE ATT&CK techniques and affected endpoints (PC1, PC2, WS-IT10).
Observed alerts related to file execution, process injection, and C2 communication attempts.
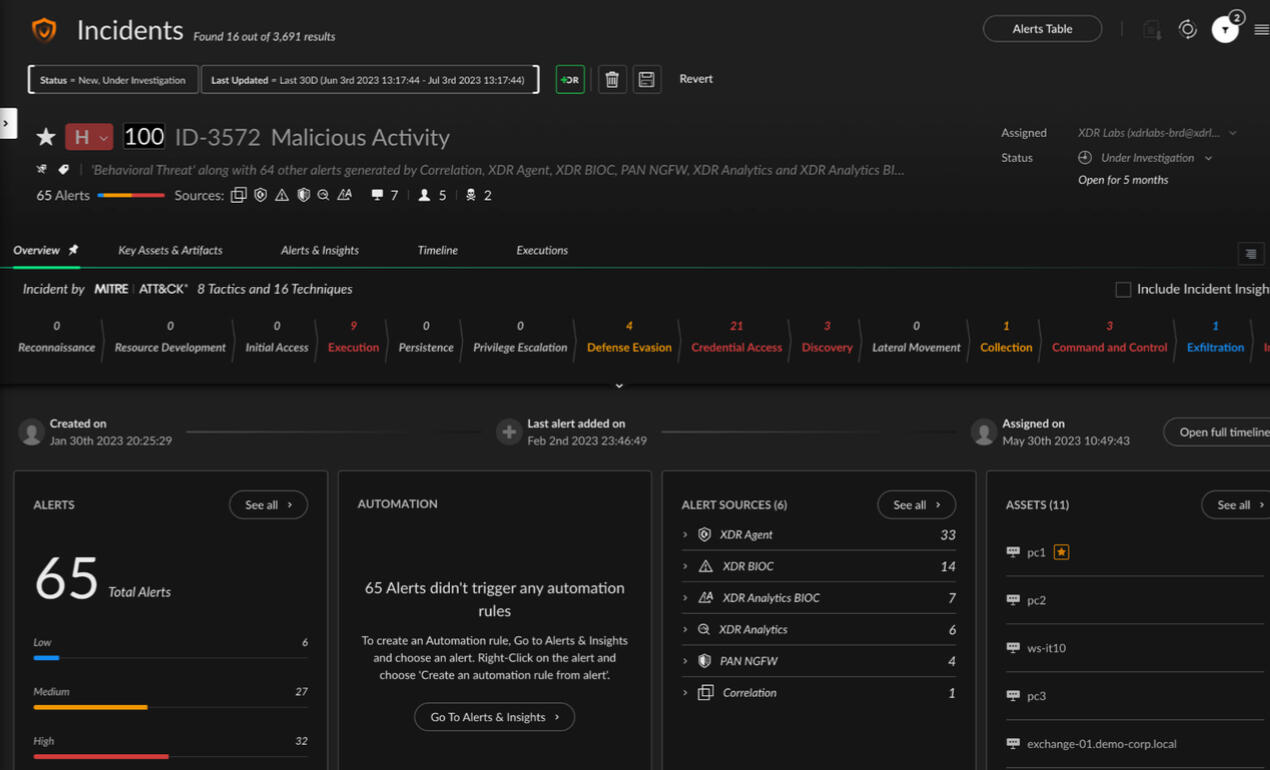
2. Timeline Analysis
Opened the Incident Timeline view to analyze when each event occurred — including phishing delivery, execution of AvengersEndgame.mp4.exe, and credential dumping activity.
This provided a visual chain of how the attack spread laterally through the environment.
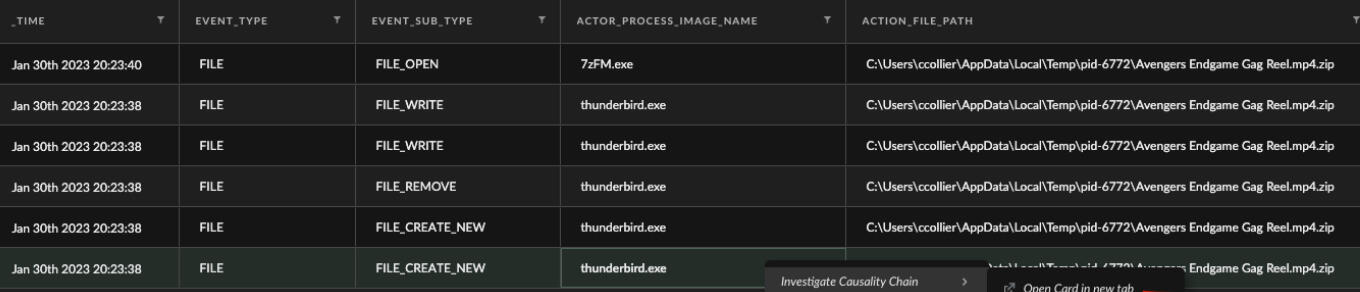
3. Root Cause Analysis with XQL
Used XQL Search to find the original infection vector.
Executed a query that filtered all file activity where the filename contained “Avengers Endgame Gag Reel.mp4.zip.”
This revealed the file was extracted and executed through Thunderbird, confirming a spear-phishing entry point.
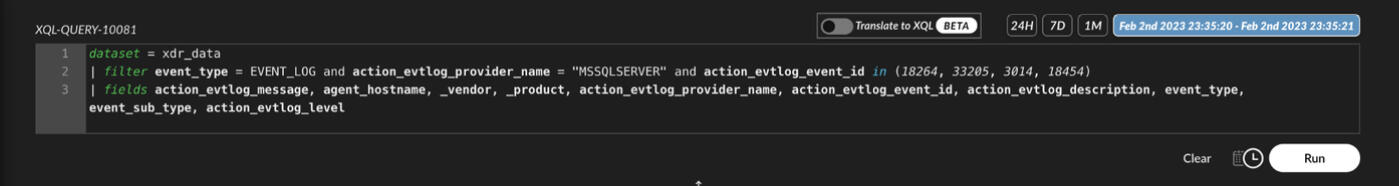
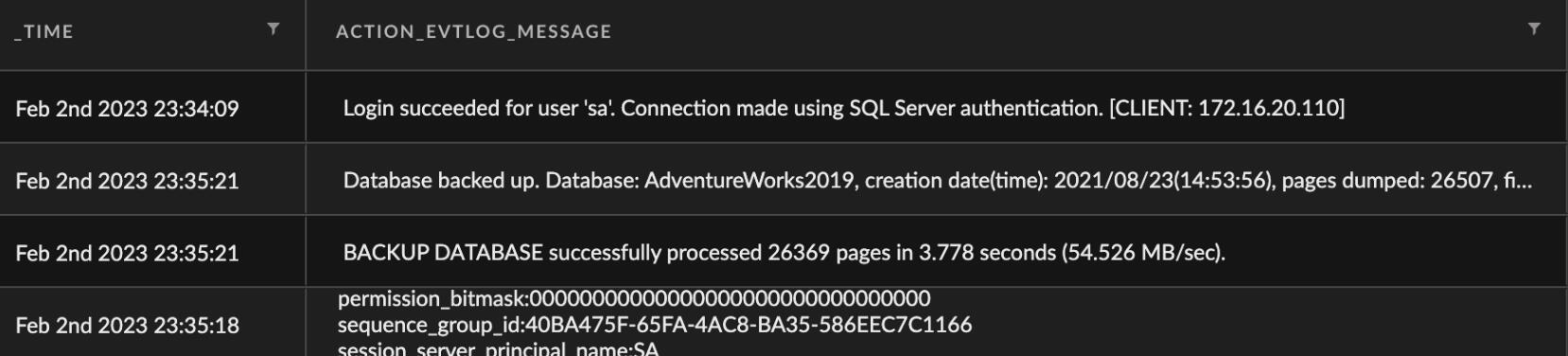
4. Correlation & Exfiltration Analysis
Reviewed Correlation Alerts for MSSQL backup and network data transfer activity to external IPs.
This confirmed data exfiltration behavior and endpoint compromise.
Outcome
Demonstrated the ability to perform a complete end-to-end investigation using Cortex XDR, from alert detection to root cause analysis and impact scoping.
Gained hands-on experience with:
- SOC workflows (alert triage, timeline reconstruction, and investigation)
- XQL querying and data correlation
- Threat hunting using behavioral analytics and MITRE ATT&CK mappingSkills Gained: Threat analysis, XQL data querying, incident triage, root cause investigation